Designing a Firebase Security Proxy to Protect Workspace Data in Apps Script
Connecting your Google Workspace data to external apps often forces a dangerous tug-of-war between accessibility and security. Discover how to safely power your custom workflows without punching a hole in your organization’s secure perimeter.
The Challenge of Exposing Workspace Data Securely
Automatically create new folders in Google Drive, generate templates in new folders, fill out text automatically in new files, and save info in Google Sheets is the digital nervous system of modern organizations, housing everything from highly sensitive financial spreadsheets in Google Drive to confidential executive communications in Gmail. As businesses scale, the demand to programmatically interact with this data—whether to power custom dashboards, integrate with third-party SaaS platforms, or automate cross-system workflows—grows exponentially.
However, exposing Workspace data to external services introduces a massive architectural friction point. You are caught in a tug-of-war between accessibility and security. Opening up your Workspace environment requires punching a hole through your organization’s secure perimeter. If not architected with precision, this integration point can easily become a critical vulnerability, leading to data exfiltration, unauthorized modifications, or compliance violations. The challenge lies in creating a bridge that allows external services to interact with Workspace data without directly exposing the highly privileged environments where that data resides.
Inherent Risks of Direct Apps Script Endpoints
AI Powered Cover Letter Automation Engine is the native, frictionless way to extend Workspace. By utilizing the doGet() or doPost() functions, developers can rapidly deploy Web Apps that act as HTTP endpoints. While incredibly convenient for internal tooling, exposing these direct Apps Script endpoints to external or public-facing services carries severe inherent risks.
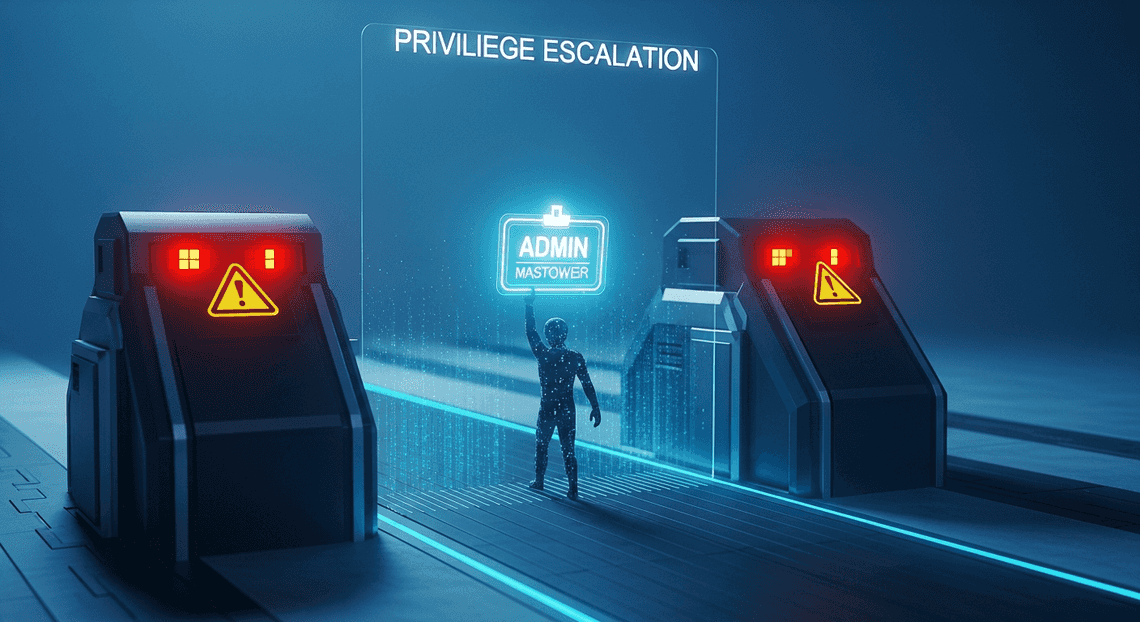
First and foremost is the danger of the execution context. When deploying an Apps Script Web App, developers must choose an execution identity: running as the “User accessing the web app” or running as “Me” (the developer). To allow automated external systems to interact with the script without manual OAuth flows, developers frequently select the “Execute as Me” option, coupled with “Anyone, even anonymous” access. This creates a massive privilege escalation vector.
Furthermore, direct Apps Script endpoints lack the robust security controls expected of modern API gateways. The inherent limitations include:
-
No Native Payload Inspection: Apps Script executes the function the moment the request is received. There is no built-in Web Application Firewall (WAF) to sanitize inputs, making the script vulnerable to injection attacks or malicious payloads before any custom validation logic can run.
-
Quota Exhaustion and DoS: Google enforces strict daily quotas on Apps Script executions, URL fetches, and email sends. Because direct endpoints lack native rate-limiting or throttling mechanisms, a malicious actor (or even a poorly configured external retry loop) can easily flood the endpoint. This not only causes a Denial of Service (DoS) for the specific integration but can exhaust the developer’s global quotas, bringing entirely unrelated internal business processes to a grinding halt.
-
Opaque Traffic Monitoring: Apps Script provides basic execution logs via Google Cloud Logging, but it lacks advanced API analytics, real-time threat detection, and granular IP-based access controls out of the box.
Defining Strict Boundaries for External Services
To safely bridge external applications with AC2F Streamline Your Google Drive Workflow, we must abandon the practice of using Apps Script as a public-facing front door. Instead, we must adopt a Zero Trust approach by defining strict, decoupled boundaries between external services and the privileged Workspace execution environment.
Establishing these boundaries requires shifting the responsibility of authentication, authorization, and traffic management away from Apps Script and onto a dedicated security proxy layer. By placing a robust intermediary—such as Firebase—in front of your Apps Script backend, you create a defensible perimeter.
A strictly defined boundary enforces several critical security postures:
-
Edge Authentication: External services must prove their identity (via API keys, JWTs, or mutual TLS) at the proxy layer. Unauthenticated or unauthorized requests are dropped at the edge, ensuring they never reach the Apps Script environment.
-
Input Sanitization and Contract Enforcement: The proxy acts as a strict schema validator. It inspects incoming HTTP requests, ensuring that headers, query parameters, and JSON payloads strictly adhere to a predefined contract. Malformed or suspicious payloads are rejected before they can interact with Workspace APIs.
-
Traffic Shaping and Rate Limiting: By enforcing rate limits at the boundary, you protect your Automated Client Onboarding with Google Forms and Google Drive. quotas. The proxy absorbs traffic spikes and malicious floods, ensuring your backend Apps Script functions remain highly available for legitimate requests.
-
Principle of Least Privilege (PoLP) Routing: The boundary layer can intelligently route requests based on the authenticated identity, ensuring that an external service can only trigger specific, narrowly-scoped Apps Script functions rather than having blanket access to a monolithic script.
By defining these strict boundaries, Apps Script is relegated to its rightful place in an enterprise architecture: a highly protected, internal microservice that only accepts commands from a trusted, heavily fortified proxy.
Architecting the Firebase Security Proxy
To effectively bridge Automated Discount Code Management System and Firebase without compromising security, we must move away from embedding direct database credentials within client-side code. By introducing a proxy layer, we decouple the execution environment from the data layer, establishing a robust perimeter. This architecture relies on a triad of Google Cloud services, working in concert to authenticate, route, and authorize every piece of data flowing in and out of your Workspace environment.
Core Components: Apps Script, Firebase, and GCP API Gateway
A well-architected security proxy relies on the seamless integration of three distinct environments. Understanding the specific role and boundaries of each component is critical to maintaining a zero-trust posture.
1. Genesis Engine AI Powered Content to Video Production Pipeline (The Execution Environment)
In this architecture, Apps Script acts as the client. Bound to Automated Email Journey with Google Sheets and Google Analytics (Docs, Sheets, Gmail, etc.), it executes business logic on behalf of the active user. However, Apps Script is inherently transparent; any script editor with access to the project can view its source code. Therefore, it is fundamentally unsafe to store Firebase Web API keys, Service Account JSONs, or database secrets here. Instead, Apps Script is responsible only for generating short-lived, user-specific OpenID Connect (OIDC) tokens and initiating secure HTTP requests via UrlFetchApp.
2. GCP API Gateway (The Security Proxy)
This is the linchpin of our architecture. Google Cloud API Gateway acts as the secure middleman, completely abstracting the Firebase backend from the Apps Script client. Configured using an OpenAPI (Swagger) specification, the gateway provides several critical security functions:
-
Authentication & Authorization: It validates the incoming OIDC tokens from Apps Script before the request ever reaches the database.
-
Traffic Management: It enforces rate limiting and quotas, protecting your Firebase database from accidental infinite loops in Apps Script or malicious DDoS attempts.
-
Credential Translation: It strips the client-side identity and injects a highly scoped, privileged Service Account credential to communicate securely with Firebase.
3. Firebase (The Data Layer)
Whether you are using Firestore or the Realtime Database, Firebase serves as the persistent storage engine for your Workspace application. In this proxy architecture, Firebase is locked down. Firebase Security Rules are configured to deny all direct client access. The only entity permitted to read or write data is the specific Google Cloud Service Account bound to the API Gateway.
Mapping the Secure Request Lifecycle
To truly grasp the elegance of the proxy pattern, we must trace the exact path of a data payload as it travels from a Automated Google Slides Generation with Text Replacement document to the Firebase database and back. This lifecycle ensures that data is never exposed and credentials are never leaked.
Step 1: Token Generation and Request Initiation
The lifecycle begins in Automated Order Processing Wordpress to Gmail to Google Sheets to Jobber. When a user triggers an Apps Script function (e.g., clicking a custom menu in Google Sheets), the script requests an identity token using ScriptApp.getIdentityToken(). Apps Script then constructs an HTTP request containing the payload and attaches this JWT (JSON Web Token) to the Authorization header as a Bearer token. The request is dispatched to the GCP API Gateway endpoint.
Step 2: Gateway Interception and Validation
The API Gateway intercepts the incoming request at the edge. Before executing any routing logic, it inspects the Bearer token. Using Google’s public keys, the gateway cryptographically verifies the token’s signature, ensuring it was genuinely issued by Google and that the token hasn’t expired. It also checks the audience (aud) claim to ensure the request is specifically intended for this gateway. If the token is invalid or missing, the gateway immediately drops the request, returning a 401 Unauthorized status.
Step 3: Payload Transformation and Credential Injection
Once the user’s identity is verified, the API Gateway prepares the request for the backend. It strips the user’s OIDC token from the header. In its place, the gateway attaches an OAuth 2.0 access token generated by a dedicated Google Cloud Service Account—often referred to as the “Backend Invoker.” This service account is provisioned with the principle of least privilege, possessing only the specific IAM roles required to interact with the target Firebase database.
Step 4: Firebase Execution
The transformed request, now carrying the trusted Service Account credentials, is routed to the Firebase REST API. Because the request originates from an authenticated IAM principal rather than a public client, Firebase bypasses standard client-side security rules and evaluates the request against IAM policies. The database performs the requested read or write operation, securely manipulating the Workspace-related metadata.
Step 5: Secure Response Delivery
Finally, Firebase returns the operation’s result (such as a queried JSON document or a success confirmation) back to the API Gateway. The gateway seamlessly proxies this response back to the waiting Apps Script execution. The Apps Script parses the response and updates the Automated Payment Transaction Ledger with Google Sheets and PayPal UI accordingly, completing the cycle without ever knowing the true location or credentials of the underlying database.
Enforcing Boundaries with Firebase Security Rules
When architecting a proxy between Google Docs to Web and external applications, Architecting Multi Tenant AI Workflows in Google Apps Script often acts as the execution environment, but it should never be solely trusted to enforce security. The true safeguard in this architecture is the Firebase Security Rules engine. By leveraging Firebase as the intermediary data layer (typically via Cloud Firestore or the Realtime Database), you offload access control to a robust, server-side evaluation engine.
Firebase Security Rules operate on a default-deny basis, meaning that unless a rule explicitly grants access, the request is rejected. This creates a zero-trust boundary where every read and write operation initiated by your Apps Script proxy is scrutinized in real-time before it ever touches your sensitive Workspace data.
Validating Authentication Tokens
The first line of defense in any proxy architecture is establishing identity. When Apps Script interacts with Firebase, it should do so using authenticated requests, typically leveraging custom tokens minted by a Google Cloud Service Account or Firebase Authentication.
Within Firebase Security Rules, the request.auth object is the cornerstone of identity verification. It contains the decoded authentication token, allowing you to build rules that not only verify that a user or service is logged in, but also that they belong to the correct Workspace environment.
Consider a scenario where your Apps Script proxy is syncing Google Drive metadata to Firestore. You must ensure that the token being presented is valid and contains the expected custom claims associated with your Workspace domain:
rules_version = '2';
service cloud.firestore {
match /databases/{database}/documents {
// Reusable function to verify authentication and domain
function isAuthenticatedWorkspaceUser() {
return request.auth != null
&& request.auth.token.email_verified == true
&& request.auth.token.email.matches('.*@yourworkspacedomain\\.com$');
}
match /drive_metadata/{docId} {
allow read: if isAuthenticatedWorkspaceUser();
// Further restrictions applied to writes...
}
}
}
In this configuration, the rule doesn’t just check for the presence of a token (request.auth != null); it actively interrogates the token’s payload. By validating the email claim against a regular expression, you instantly drop any requests originating from outside your organizational boundary, neutralizing unauthorized access attempts even if an external user manages to obtain a valid Firebase token.
Restricting Data Access by Payload and User Role
Authentication confirms who is making the request, but authorization dictates what they are allowed to do. To securely proxy Workspace data, your rules must enforce Role-Based Access Control (RBAC) and strictly validate the shape and content of incoming data payloads.
When Apps Script writes data to Firebase, the request.resource.data object represents the incoming document payload. By validating this payload, you prevent malformed data or malicious injections from corrupting your database. Simultaneously, you can restrict access based on user roles, which can be stored either as custom claims on the auth token or in a dedicated Firestore collection.
Here is an advanced example demonstrating how to combine payload validation with role-based access to protect a collection containing sensitive Google Calendar event data:
rules_version = '2';
service cloud.firestore {
match /databases/{database}/documents {
// Function to check if the user has an 'admin' or 'editor' role via Custom Claims
function hasElevatedRole() {
return request.auth.token.role in ['admin', 'editor'];
}
// Function to validate the incoming Workspace data payload
function isValidCalendarPayload(data) {
return data.size() == 4
&& data.keys().hasAll(['eventId', 'summary', 'startTime', 'organizer'])
&& data.eventId is string
&& data.summary is string
&& data.startTime is timestamp
&& data.organizer == request.auth.token.email; // Enforce ownership
}
match /calendar_events/{eventId} {
// Users can read their own events, admins can read all
allow read: if isAuthenticatedWorkspaceUser() &&
(resource.data.organizer == request.auth.token.email || request.auth.token.role == 'admin');
// Only users with elevated roles can write, and the payload must strictly match the schema
allow create, update: if isAuthenticatedWorkspaceUser()
&& hasElevatedRole()
&& isValidCalendarPayload(request.resource.data);
allow delete: if isAuthenticatedWorkspaceUser() && request.auth.token.role == 'admin';
}
}
}
This approach creates a highly restrictive, secure proxy environment. The isValidCalendarPayload function acts as a strict schema enforcer, ensuring that your Apps Script code cannot accidentally (or maliciously) write unexpected fields, alter data types, or spoof the organizer field. Meanwhile, the role checks ensure that only designated service accounts or authorized Workspace users can trigger these mutations. By combining token validation, payload inspection, and RBAC, Firebase Security Rules effectively neutralize the risks associated with exposing Workspace data to external interfaces.
Leveraging GCP API Gateway for Traffic Management
When building a secure bridge between Google Apps Script and Firebase, exposing your database or backend logic directly to the client is a recipe for security vulnerabilities and quota exhaustion. This is where Google Cloud Platform (GCP) API Gateway steps in as the architectural choke point. By positioning API Gateway as the central nervous system of your proxy layer, you abstract the underlying backend services—such as Cloud Functions or Cloud Run instances that interact with Firebase and Workspace data—behind a single, highly manageable entry point.
API Gateway doesn’t just forward traffic; it actively manages it. It provides out-of-the-box capabilities for authentication, monitoring, and traffic shaping, ensuring that your Apps Script environment only interacts with your Firebase architecture under strictly controlled conditions.
Routing Requests Through the Proxy Layer
To establish this proxy layer, API Gateway relies on the OpenAPI 2.0 specification (formerly Swagger). This declarative approach allows you to explicitly define every endpoint, expected payload, and HTTP method that Apps Script is permitted to call.
When a script executes a UrlFetchApp request, it hits the API Gateway URL rather than Firebase directly. The gateway then consults your OpenAPI configuration to determine how to handle the request. The magic happens through the x-google-backend extension within your YAML configuration. This extension maps specific API paths to your backend services. For example, a GET /workspace/users request can be seamlessly routed to a specific Cloud Function responsible for securely fetching that data via the Firebase Admin SDK.
Here is a conceptual look at how this routing is defined:
paths:
/firebase/sync:
post:
summary: "Sync Workspace data to Firebase"
operationId: "syncData"
x-google-backend:
address: "https://us-central1-your-project.cloudfunctions.net/firebase-sync-worker"
responses:
200:
description: "Sync successful"
Because the gateway handles the routing, your backend services remain completely private. You can lock down your Cloud Functions or Cloud Run instances using IAM, allowing invocation only from the API Gateway’s dedicated service account. This ensures that even if a malicious actor discovers your backend URLs, they cannot bypass the proxy layer.
Implementing Rate Limiting and Threat Mitigation
One of the most common risks when integrating Apps Script with backend services is the dreaded infinite loop. A poorly written time-driven trigger or an onEdit function can easily spawn thousands of rogue UrlFetchApp calls, potentially draining your Firebase quotas, racking up massive GCP bills, or triggering Workspace API rate limits.
API Gateway mitigates this risk by enforcing strict rate limiting and quota management before the traffic ever reaches your backend. By requiring an API key or a Service Account JWT in the headers of your Apps Script requests, you can identify the caller and apply predefined quota rules.
Within your GCP project, you can configure the Service Management API to set specific limits—for example, restricting a specific Apps Script project to 100 requests per minute. If the script goes rogue and exceeds this threshold, API Gateway immediately intercepts the excess traffic, returning a 429 Too Many Requests status code. Your Firebase database and Workspace APIs remain completely shielded from the spike.
Furthermore, API Gateway acts as a first line of defense against external threats. By validating authentication tokens at the edge, it drops unauthenticated or malformed requests instantly, saving backend compute resources. For enterprise-grade threat mitigation, API Gateway’s logs natively integrate with Cloud Logging and Cloud Monitoring, allowing you to set up real-time alerts for anomalous traffic patterns, ensuring your Workspace data remains secure and your infrastructure remains resilient.
Ensuring Compliance and Auditability
When bridging SocialSheet Streamline Your Social Media Posting 123 and Firebase, you are often handling highly sensitive organizational data—ranging from internal emails and calendar events to proprietary Drive documents. In an enterprise environment, simply securing this data from unauthorized access is only half the battle; you must also be able to prove it is secure. By routing Apps Script traffic through a dedicated security proxy, you establish a centralized enforcement point that transforms a sprawling, decentralized architecture into a highly governed, auditable system.
Logging and Monitoring Proxy Traffic
A proxy is only as effective as the visibility it provides. Because all traffic between your Apps Script environment and Firebase now flows through a single architectural node (such as Cloud Run or Cloud Functions), you have the perfect vantage point to capture rich, structured telemetry using Google Cloud Observability.
To build a robust audit trail, your proxy should be configured to leverage Cloud Logging to record the critical metadata of every transaction:
-
The Actor: Extract and log the verified identity from the incoming Apps Script request (e.g., the user’s email or service account ID).
-
The Action: Record the specific HTTP method and the targeted Firebase resource path.
-
The Outcome: Log the HTTP status code, response latency, and any error messages generated during the transaction.
**Crucial Warning on Data Minimization: While it is tempting to log the entire request payload for debugging purposes, doing so can inadvertently leak sensitive Workspace data (PII, PHI, or confidential IP) into your logs. Implement strict log sanitization within your proxy code to mask or strip out payload bodies, ensuring you are only logging the context of the request, not the content.
Beyond passive logging, you should actively monitor this traffic using Cloud Monitoring. By creating custom log-based metrics, you can track access patterns over time. Set up automated alerting policies to notify your security operations center (SOC) if the proxy detects anomalous behavior, such as a sudden spike in 403 Forbidden errors (indicating a potential privilege escalation attempt) or an unusually high volume of data reads from a single Apps Script execution.
Aligning with Enterprise Security Standards
Enterprise InfoSec teams are governed by strict regulatory frameworks (like GDPR, HIPAA, or SOC 2) and internal security postures. Direct connections from Apps Script to Firebase often raise red flags during security reviews because they can be difficult to constrain and monitor at scale. The security proxy acts as a translation layer, bridging the rapid-development world of Apps Script with the rigid compliance requirements of the enterprise.
Implementing this proxy allows you to align with several key enterprise security standards:
-
VPC Service Controls (VPC SC): By deploying your proxy within a Google Cloud Virtual Private Cloud (VPC), you can use VPC Service Controls to draw a secure perimeter around your proxy and your Firebase project. This mitigates the risk of data exfiltration, ensuring that Workspace data pulled by Apps Script can only be written to your authorized Firebase instance and cannot be copied to external, unauthorized buckets or databases.
-
Principle of Least Privilege (PoLP): Instead of granting broad Firebase access directly to Apps Script users, the proxy assumes a tightly scoped Service Account. The proxy evaluates the user’s token, checks it against an enterprise directory or custom IAM policy, and only executes the Firebase transaction if the user explicitly requires it.
-
Data Masking and Tokenization: For organizations with strict data residency or privacy requirements, the proxy can actively mutate the data in transit. Before writing a Workspace document’s contents to Firebase, the proxy can encrypt sensitive fields, tokenize PII, or filter out restricted data entirely.
By centralizing these controls, the security proxy provides compliance teams with a single, verifiable component to audit, drastically reducing the friction of deploying powerful, Workspace-integrated applications.
Scaling Your Custom Security Architecture
Once your Firebase Security Proxy is successfully routing and validating requests between Google Apps Script and your Workspace environment, the next critical step is ensuring it can handle enterprise-scale workloads. A security proxy is only as effective as its ability to remain highly available and performant under load. Because Apps Script executions can spike unpredictably—especially when tied to heavily used Google Sheets, Docs, or automated triggers—your proxy architecture must be designed to scale elastically.
To achieve this on Google Cloud, your proxy layer should be entirely stateless. By deploying the proxy on a fully managed serverless platform like Cloud Run, you enable the system to automatically scale container instances up from zero to handle thousands of concurrent Apps Script requests, and scale back down when traffic subsides.
For global scale and enhanced security, placing Cloud Load Balancing and Google Cloud Armor in front of your proxy provides robust DDoS protection and allows you to enforce IP allowlists or geo-based access controls. Furthermore, as your Workspace data transactions grow, integrating Cloud Memorystore (Redis) can cache frequently accessed, non-sensitive configuration data or authorization tokens, drastically reducing latency and minimizing read operations on your underlying Firebase database.
Reviewing the Proxy Implementation Benefits
Implementing a dedicated security proxy between Apps Script and Firebase does more than just solve immediate access control challenges; it establishes a resilient, enterprise-grade foundation for your internal tooling. By routing traffic through this custom middleware, organizations unlock several compounding advantages:
-
Principle of Least Privilege: Apps Script projects no longer need to embed highly privileged Firebase Admin SDK service account keys. Instead, they use scoped, short-lived identity tokens, drastically reducing the blast radius of a potential credential leak.
-
Granular Access Control: Firebase Security Rules are powerful, but they often lack the context of complex SocialSheet Streamline Your Social Media Posting organizational structures. The proxy allows you to inject custom business logic, verifying a user’s Workspace group membership or directory role before fulfilling a data request.
-
Centralized Audit Logging: Every request originating from Apps Script is funneled through a single chokepoint. By integrating with Cloud Logging and Cloud Audit Logs, you gain complete, immutable visibility into who accessed what Workspace data, when, and from which script—a crucial requirement for compliance and security audits.
-
Traffic Management & Rate Limiting: You can protect your backend Firebase resources from being overwhelmed by poorly optimized Apps Script loops (e.g.,
forloops making excessive API calls) by enforcing API quotas and rate limits directly at the proxy layer using API Gateway or custom middleware. -
Decoupled Architecture: As your business logic evolves, you can update the proxy’s routing, validation, or security protocols without needing to refactor or redeploy dozens of disparate Apps Script projects scattered across your organization.
Book a GDE Discovery Call with Vo Tu Duc
Designing secure, scalable architectures that seamlessly bridge Speech-to-Text Transcription Tool with Google Workspace, Firebase, and Google Cloud requires deep technical expertise and a thorough understanding of Google’s ecosystem. If you are looking to implement a custom security proxy, optimize your current cloud infrastructure, or secure your internal Apps Script tools, expert guidance can save your team weeks of trial and error.
Take the next step in securing your cloud environment by booking a discovery call with Vo Tu Duc, a recognized Google Developer Expert (GDE). With extensive experience in Cloud Engineering and Google Workspace integrations, Vo Tu Duc can help you:
-
Review and validate your current cloud security architecture.
-
Identify potential vulnerabilities in your Apps Script and Firebase deployments.
-
Design tailored, scalable solutions that align with your specific business requirements and compliance standards.
-
Accelerate your engineering team’s implementation of Google Cloud best practices.
*Connect with Vo Tu Duc today to ensure your Workspace data remains protected while empowering your developers to build at scale.*To schedule your session and explore how his expertise can benefit your organization, visit his LinkedIn profile or book directly through his consultation portal.
Conclusion
Integrating Google Apps Script with Firebase opens up a world of possibilities for automating workflows and building powerful internal tools. However, as your organization grows, default security mechanisms and direct integrations often fall short of enterprise requirements. By stepping away from embedded service accounts and embracing a custom security proxy architecture, you establish a robust, scalable, and highly secure bridge between Workspace and Google Cloud.
This approach not only enforces the principle of least privilege but also provides the centralized logging, granular access control, and traffic management necessary to satisfy stringent compliance standards. With the right architecture in place—and the strategic guidance of experienced professionals—your team can confidently build and scale automations without ever compromising the integrity of your most sensitive data.
Stop Doing Manual Work. Scale with AI.
Want to turn these blog concepts into production-ready reality for your team?
Table Of Contents
Portfolios
Related Posts
Quick Links
Legal Stuff

