Secure PII in AI Pipelines Using Regex and the Gemini API
As organizations rush to integrate generative AI, feeding unfiltered data into LLMs creates a critical choke point for catastrophic privacy leaks. Discover why robust data sanitization is no longer optional, but a foundational pillar of modern cloud architecture.
The Critical Need for Data Privacy in AI Workflows
As organizations rush to integrate generative AI into their applications, the architecture of data pipelines is undergoing a fundamental shift. Cloud engineers are no longer just moving data from databases to analytics engines; they are now orchestrating complex workflows where raw, unstructured data is fed directly into Large Language Models (LLMs). While tools like the Gemini API unlock incredible capabilities for summarization, entity extraction, and content generation, they also introduce a critical choke point for data privacy. Injecting unfiltered data into an AI pipeline without a robust sanitization strategy is a recipe for catastrophic data leaks. In modern cloud engineering, treating data privacy as an afterthought is not an option—it must be a foundational pillar of your AI architecture.
Understanding the Risks of Exposing PII to LLMs
Personally Identifiable Information (PII)—such as Social Security numbers, email addresses, financial records, and medical histories—is the most sensitive asset an organization holds. When this data is inadvertently passed to an LLM during inference or fine-tuning, the security risks multiply exponentially.
First, there is the risk of data persistence and model memorization. While enterprise-grade services like Google Cloud’s Building Self Correcting Agentic Workflows with Vertex AI ensure that your prompt data is not used to train foundational models by default, the broader pipeline often includes intermediate logging, caching layers, or custom fine-tuning jobs. If PII is captured in Cloud Storage buckets used for prompt logging, or accidentally baked into a custom model’s weights during tuning, it creates a persistent vulnerability where sensitive data could be regurgitated in response to adversarial prompt injection attacks.
Second, exposing unredacted PII unnecessarily expands your attack surface. Modern AI pipelines are highly distributed, often involving multiple microservices, serverless compute instances (like Cloud Run or Cloud Functions), and message brokers (like Pub/Sub). Every time a payload containing unredacted PII traverses these network boundaries to reach an LLM endpoint, it increases the risk of exposure through compromised audit logs or insider threats. Cloud security demands operating under the principle of least privilege, ensuring that the LLM only receives the exact semantic context it needs to perform its task—and absolutely nothing more.
Compliance and Regulatory Demands for Security Engineers
Beyond the technical vulnerabilities, the mishandling of PII in AI workflows triggers severe legal and financial repercussions. Regulatory frameworks such as the General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), and the Health Insurance Portability and Accountability Act (HIPAA) impose strict mandates on how user data is processed, stored, and transmitted.
For security and cloud engineers, these regulations translate into rigid architectural requirements. You are tasked with enforcing data minimization—the practice of limiting data processing to only what is strictly necessary for the stated purpose. For example, if an AI agent powered by Gemini is designed to summarize customer support tickets or analyze sentiment, it requires the context of the conversation, not the customer’s credit card number or home address.
Furthermore, compliance auditors require comprehensive visibility into data lineage and boundary enforcement. If raw PII is sent to an external API, it drastically complicates compliance audits and data processing agreements. Engineers must implement verifiable, deterministic sanitization steps before the data ever leaves the trusted boundary of their Virtual Private Cloud (VPC). By proactively stripping PII at the pipeline’s ingress—using reliable methods like Regex combined with Google Cloud’s Data Loss Prevention (DLP) strategies—organizations can maintain strict compliance, simplify their audit trails in Cloud Logging, and empower developers to build innovative AI solutions without running afoul of regulatory demands.
Designing a Secure Pre Processing Architecture
When integrating Large Language Models (LLMs) into enterprise workflows, security cannot be an afterthought—it must be the foundation of your architecture. Sending raw, unfiltered documents directly to an external API introduces significant compliance risks, especially when dealing with Personally Identifiable Information (PII) such as social security numbers, financial records, or private contact details. To mitigate this, we must design a secure pre-processing architecture that acts as a robust firewall between your sensitive data and the AI model.
By leveraging the native capabilities of Automatically create new folders in Google Drive, generate templates in new folders, fill out text automatically in new files, and save info in Google Sheets and Google Cloud, we can build a serverless, highly scalable pipeline that sanitizes data locally before it ever leaves your secure environment.
Core Components AI Powered Cover Letter Automation Engine Document App and Gemini
To build this secure pipeline, we will orchestrate three primary components within the Google ecosystem. Each plays a distinct role in ensuring that our data remains secure, accessible, and intelligently processed:
-
**Genesis Engine AI Powered Content to Video Production Pipeline (GAS): This is the serverless orchestration engine of our architecture. Running entirely within Google’s secure cloud infrastructure, Apps Script allows us to execute backend logic without provisioning servers. Crucially, this is where our Regex-based sanitization engine will live. Because GAS executes within the trusted boundary of your AC2F Streamline Your Google Drive Workflow tenant, the PII is processed and masked before any external HTTP requests are made.
-
Google Document App Service: This service acts as our data ingestion point. Using the
DocumentAppclass, we can programmatically access, read, and manipulate Google Docs. It serves as the bridge between the unstructured raw text provided by the user and the structured pipeline managed by Apps Script. It also allows us to write the final, AI-generated output back into a familiar interface for the end-user. -
The Gemini API: Google’s highly capable multimodal AI model serves as the cognitive engine of our pipeline. While Gemini is designed with enterprise-grade security, best practices dictate the principle of least privilege: the model should only receive the data it absolutely needs to perform its task. By the time the payload reaches the Gemini API, all sensitive entities will have been replaced by generic, non-identifiable tokens.
Mapping the Data Flow from Raw Text to Anonymization
A well-architected pipeline relies on a strictly linear and predictable data flow. To guarantee that no PII leaks into the AI inference stage, the data must transition through four distinct phases:
-
Ingestion and Extraction: The pipeline is triggered (either manually via a custom Google Docs menu or automatically via a Workspace trigger). The
DocumentAppservice reads the active document, extracting the raw text body into the Apps Script memory space. At this stage, the text contains highly sensitive, unmasked PII. -
Local Sanitization (The Regex Firewall): This is the critical security checkpoint. Before any network requests are initiated to the Gemini API, the raw text is passed through a series of compiled Regular Expressions within Apps Script. These Regex patterns are meticulously crafted to identify standard PII formats (e.g.,
\b\d{3}-\d{2}-\d{4}\bfor SSNs). Once identified, the script dynamically replaces these strings with standardized placeholder tokens (e.g.,[REDACTED_SSN],[REDACTED_EMAIL]). -
Secure AI Inference: The newly anonymized text—now completely stripped of its sensitive data—is packaged into a JSON payload. Apps Script uses the
UrlFetchAppservice to securely transmit this sanitized prompt to the Gemini API. Gemini processes the text, performing tasks such as summarization, How to build a Custom Sentiment Analysis System for Operations Feedback Using Google Forms AppSheet and Vertex AI, or entity extraction, using only the context provided by the safe tokens. -
**Delivery and Re-integration: The Gemini API returns its generated response to the Apps Script environment. Depending on the specific use case, the script can either safely write this response directly back into the Google Doc via
DocumentApp, or, if a mapping dictionary was temporarily stored during Step 2, safely re-inject the original PII into the final output locally before presenting it to the user.
By enforcing this strict, unidirectional flow from extraction to local Regex sanitization, we ensure that the Gemini API delivers powerful AI capabilities without ever compromising the integrity or confidentiality of your user data.
Extracting and Sanitizing Document Text
When building enterprise-grade AI pipelines, the data ingestion phase is your first and most critical security checkpoint. Before a single token is processed by the Gemini API, raw data must be extracted from its source and rigorously scrubbed of Personally Identifiable Information (PII). In a Automated Client Onboarding with Google Forms and Google Drive. environment, this means safely interfacing with the Google Docs API and applying deterministic text sanitization techniques to ensure sensitive data never reaches the language model.
Securely Reading Data via Google Docs API
To programmatically access documents, the Google Docs API is our primary integration point. However, as Cloud Engineers, we must prioritize security at the Identity and Access Management (IAM) level. Instead of using overly permissive credentials, you should employ a Service Account or standard OAuth 2.0 flows restricted by the principle of least privilege. Ensure your OAuth scopes are strictly limited to https://www.googleapis.com/auth/documents.readonly so the pipeline cannot inadvertently modify or delete files.
Extracting text from a Google Doc requires parsing the document’s underlying JSON structure. A document is represented as a JSON object containing body elements, which in turn contain paragraph and textRun objects.
Here is a JSON-to-Video Automated Rendering Engine snippet demonstrating how to securely authenticate and extract raw text using the official Google API client:
from google.oauth2 import service_account
from googleapiclient.discovery import build
# 1. Authenticate using least-privilege service account credentials
SCOPES = ['https://www.googleapis.com/auth/documents.readonly']
creds = service_account.Credentials.from_service_account_file(
'path/to/service_account.json', scopes=SCOPES)
# 2. Build the Docs service client
docs_service = build('docs', 'v1', credentials=creds)
def extract_text_from_doc(document_id):
"""Securely extracts raw text from a Google Doc."""
doc = docs_service.documents().get(documentId=document_id).execute()
content = doc.get('body').get('content', [])
extracted_text = ""
for element in content:
if 'paragraph' in element:
elements = element.get('paragraph').get('elements', [])
for elem in elements:
if 'textRun' in elem:
extracted_text += elem.get('textRun').get('content', '')
return extracted_text
This approach ensures that your pipeline only reads what it explicitly has access to, keeping the data extraction phase hermetically sealed and highly performant.
Building Rigorous Regex Patterns for SSNs and Bank Accounts
Once the raw text is extracted, it must be sanitized before being passed to the Gemini API. While Large Language Models are incredibly capable, relying solely on them to identify and redact PII is a dangerous anti-pattern due to hallucination risks and prompt injection vulnerabilities. Regular Expressions (Regex) provide a deterministic, computationally inexpensive, and highly reliable first line of defense.
When dealing with highly sensitive financial and personal data, your regex patterns must be rigorous to avoid false negatives (missing PII) while minimizing false positives (redacting benign data like product IDs).
Social Security Numbers (SSNs):
A standard US SSN follows the XXX-XX-XXXX format. A naive regex might simply look for \d{3}-\d{2}-\d{4}. However, a robust pattern accounts for invalid SSN ranges (for example, SSNs cannot start with 000, 666, or 900-999, and the middle or end sections cannot be all zeros).
Bank Account and Routing Numbers:
Bank accounts are notoriously tricky as their lengths vary, typically between 8 and 12 digits in the US, while routing numbers are exactly 9 digits. To prevent aggressively redacting every 9-digit number (which could be a zip code extension or an internal database ID), context-aware regex using boundary matching and lookarounds is highly recommended.
Here is how you can implement a rigorous sanitization function in Python using the re module to mask these specific patterns:
import re
def sanitize_pii(text):
"""Redacts SSNs and potential Bank Account/Routing numbers from text."""
# Rigorous SSN Pattern using negative lookaheads to exclude invalid ranges
ssn_pattern = re.compile(r'\b(?!000|666|9\d{2})\d{3}-(?!00)\d{2}-(?!0000)\d{4}\b')
# Context-aware Routing Number Pattern (9 digits)
# Looks for keywords like 'routing' or 'aba' preceding the number
routing_pattern = re.compile(r'(?i)\b(?:routing|aba)[\s#:-]*(\d{9})\b')
# Context-aware Account Number Pattern (8-12 digits)
account_pattern = re.compile(r'(?i)\b(?:account|acct)[\s#:-]*(\d{8,12})\b')
# Apply redactions
sanitized_text = ssn_pattern.sub('[REDACTED_SSN]', text)
# For bank details, we replace the captured group to maintain the surrounding context
sanitized_text = routing_pattern.sub(r'Routing: [REDACTED_ROUTING]', sanitized_text)
sanitized_text = account_pattern.sub(r'Account: [REDACTED_ACCOUNT]', sanitized_text)
return sanitized_text
By combining the secure data extraction capabilities of the Automated Discount Code Management System APIs with deterministic regex sanitization, you create a robust “data wash” layer. This ensures that the text payload ultimately handed off to your Gemini AI pipeline is stripped of critical PII, maintaining strict compliance and protecting user privacy.
Executing the Redaction Logic in Apps Script
When integrating Automated Email Journey with Google Sheets and Google Analytics applications with external AI models, Architecting Multi Tenant AI Workflows in Google Apps Script serves as the perfect serverless middleware. By intercepting user inputs or document contents within the secure boundary of your Workspace environment, Apps Script ensures that no raw data ever touches the network before being sanitized. Leveraging the V8 runtime, Apps Script allows us to execute robust, modern JavaScript to handle our redaction logic swiftly and efficiently.
Applying Regex Replacements to Intercept Sensitive Data
Regular Expressions (Regex) provide a highly efficient, pattern-matching mechanism to identify and mask Personally Identifiable Information (PII) such as email addresses, phone numbers, and Social Security Numbers. Because Apps Script runs synchronously, applying regex replacements directly in memory ensures that the data is sanitized in real-time.
To implement this, we define a series of regex patterns tailored to the specific types of PII we expect to encounter. We then utilize the JavaScript String.prototype.replace() method, combined with the global (g) flag, to ensure every instance of a pattern within the text is intercepted and replaced with a standardized placeholder.
Here is a practical implementation of how you can structure this logic in Apps Script:
/**
* Sanitizes input text by replacing PII with standardized tokens.
* @param {string} text - The raw input text containing potential PII.
* @return {string} The sanitized text.
*/
function redactPII(text) {
if (!text) return "";
// Define regex patterns for common PII
const patterns = {
email: /[a-zA-Z0-9._%+-]+@[a-zA-Z0-9.-]+\.[a-zA-Z]{2,}/g,
phone: /\b(?:\+?1[-. ]?)?\(?([0-9]{3})\)?[-. ]?([0-9]{3})[-. ]?([0-9]{4})\b/g,
ssn: /\b\d{3}-\d{2}-\d{4}\b/g
};
let sanitizedText = text;
// Apply replacements iteratively
sanitizedText = sanitizedText.replace(patterns.email, '[REDACTED_EMAIL]');
sanitizedText = sanitizedText.replace(patterns.phone, '[REDACTED_PHONE]');
sanitizedText = sanitizedText.replace(patterns.ssn, '[REDACTED_SSN]');
return sanitizedText;
}
By replacing sensitive data with explicit tokens like [REDACTED_EMAIL], we achieve two goals: we protect the user’s privacy, and we provide the Gemini API with contextual clues. The LLM still understands that an email address was present in that exact location, allowing it to maintain the semantic structure of the prompt without processing the actual sensitive data.
Validating the Anonymized Payload Before Transmission
In Cloud Engineering, relying on a single point of failure is an anti-pattern. While regex is powerful, edge cases or malformed inputs can sometimes bypass standard patterns. Therefore, before we dispatch the payload to the Gemini API using UrlFetchApp, we must implement a validation step. This acts as a failsafe, ensuring the anonymized payload is structurally sound and strictly free of the targeted PII.
Validation involves running a secondary, broader scan against the sanitized string and properly formatting the JSON payload required by the Gemini API. If the validation fails, the script should aggressively halt execution rather than risk a data leak.
/**
* Validates the sanitized text and constructs the Gemini API payload.
* @param {string} rawInput - The original user input.
* @return {string} The JSON stringified payload ready for transmission.
*/
function prepareAndValidatePayload(rawInput) {
// 1. Sanitize the input
const safePrompt = redactPII(rawInput);
// 2. Failsafe Validation: Broad check to catch missed patterns
// This regex looks for an @ symbol or a standard SSN format as a final sanity check
const failsafeRegex = /(@|\b\d{3}-\d{2}-\d{4}\b)/;
if (failsafeRegex.test(safePrompt)) {
// Log the error securely (without logging the raw input)
console.error("Security Exception: PII validation failed. Payload transmission aborted.");
throw new Error("Data sanitization failed. Please review your input.");
}
// 3. Construct the Gemini API payload
const payload = {
contents: [{
parts: [{
text: safePrompt
}]
}],
generationConfig: {
temperature: 0.2 // Keep responses deterministic for data processing tasks
}
};
// Return the validated, stringified JSON payload
return JSON.stringify(payload);
}
/**
* Example execution function to call the Gemini API
*/
function callGeminiSecurely() {
const rawData = "Please analyze this user feedback from [email protected], phone 555-123-4567.";
try {
const safePayload = prepareAndValidatePayload(rawData);
// The payload is now safe to transmit via UrlFetchApp
/*
const options = {
method: 'post',
contentType: 'application/json',
payload: safePayload
};
const response = UrlFetchApp.fetch(GEMINI_API_URL, options);
*/
console.log("Payload successfully prepared and validated.");
} catch (error) {
console.error("Execution halted: " + error.message);
}
}
By structuring your Apps Script pipeline with this two-step approach—aggressive regex redaction followed by strict validation—you establish a robust, zero-trust boundary. The data is thoroughly scrubbed inside the Automated Google Slides Generation with Text Replacement ecosystem, guaranteeing that the outbound HTTP requests to the Gemini API contain only safe, anonymized tokens.
Integrating the Gemini API Safely
With your data pipeline now successfully identifying and redacting Personally Identifiable Information (PII) using regex, the next critical phase is interfacing with the generative model. Stripping sensitive data is only half the battle; the method by which you transmit this sanitized data to the AI model must also adhere to strict cloud security standards. As a best practice, enterprise environments should leverage the Gemini API via Google Cloud’s Vertex AI, which provides robust enterprise-grade security, compliance, and data governance features out of the box.
Establishing a Secure Connection to the AI Endpoint
When building secure cloud architectures, hardcoding API keys is a cardinal sin. To establish a secure connection to the Gemini endpoint on Vertex AI, you should rely on Google Cloud Identity and Access Management (IAM) and Application Default Credentials (ADC). By assigning a dedicated Service Account with the principle of least privilege—granting only the Vertex AI User role—you ensure that your application authenticates securely without exposing long-lived credentials.
Furthermore, for strict network security, this connection should ideally be routed through a Virtual Private Cloud (VPC) using Private Google Access or VPC Service Controls. This guarantees that your traffic to the Gemini API never traverses the public internet.
Here is how you securely initialize the Vertex AI SDK in Python using ADC:
import vertexai
from google.auth import default
from google.api_core.exceptions import GoogleAPIError
# Define your Google Cloud Project and Region
PROJECT_ID = "your-secure-gcp-project"
LOCATION = "us-central1"
def initialize_secure_vertex_connection():
try:
# ADC automatically picks up the Service Account credentials from the environment
credentials, _ = default()
# Initialize the Vertex AI SDK securely
vertexai.init(
project=PROJECT_ID,
location=LOCATION,
credentials=credentials
)
print("Secure connection to Vertex AI established.")
except GoogleAPIError as e:
print(f"Failed to authenticate and connect to Vertex AI: {e}")
raise
initialize_secure_vertex_connection()
By relying on the underlying infrastructure to handle the token lifecycle, you eliminate the risk of credential leakage in your source code or CI/CD pipelines.
Processing the Sanitized Prompt and Handling the Response
Once the secure connection is established, you can safely pass your regex-sanitized prompts to the Gemini model. Because the prompt now contains placeholders (e.g., [REDACTED_EMAIL] or [USER_ID_1]) instead of actual PII, the data leaving your environment is completely anonymized.
When invoking the model, it is crucial to configure both generation parameters and Google’s built-in safety settings. Even though you have scrubbed the PII, configuring safety settings ensures the model does not generate inappropriate, harmful, or out-of-bounds content in its response.
Here is an example of how to securely process the sanitized prompt and handle the model’s response:
from vertexai.generative_models import GenerativeModel, HarmCategory, HarmBlockThreshold
def generate_safe_response(sanitized_prompt: str) -> str:
# Instantiate the Gemini model
model = GenerativeModel("gemini-1.5-pro")
# Define strict safety settings to prevent malicious or harmful outputs
safety_settings = {
HarmCategory.HARM_CATEGORY_HATE_SPEECH: HarmBlockThreshold.BLOCK_MEDIUM_AND_ABOVE,
HarmCategory.HARM_CATEGORY_DANGEROUS_CONTENT: HarmBlockThreshold.BLOCK_MEDIUM_AND_ABOVE,
HarmCategory.HARM_CATEGORY_SEXUALLY_EXPLICIT: HarmBlockThreshold.BLOCK_MEDIUM_AND_ABOVE,
HarmCategory.HARM_CATEGORY_HARASSMENT: HarmBlockThreshold.BLOCK_MEDIUM_AND_ABOVE,
}
# Define generation configuration to control the output's determinism
generation_config = {
"temperature": 0.2, # Lower temperature for more deterministic, predictable outputs
"max_output_tokens": 1024,
}
try:
# Send the sanitized prompt to the Gemini API
response = model.generate_content(
sanitized_prompt,
generation_config=generation_config,
safety_settings=safety_settings
)
# Secure logging: Log the sanitized prompt and response, NEVER the raw user input
# logger.info(f"Sanitized Prompt: {sanitized_prompt} | Response: {response.text}")
return response.text
except Exception as e:
# Handle API errors, quota limits, or blocked content gracefully
# logger.error(f"Error during Gemini API invocation: {str(e)}")
return "An error occurred while processing the request securely."
# Example usage:
# sanitized_input = "Please summarize the recent support ticket for user [REDACTED_NAME]."
# print(generate_safe_response(sanitized_input))
Handling the response correctly is just as important as sending the prompt. Ensure that your application logic gracefully catches exceptions, such as quota exhaustion or prompts blocked by Vertex AI’s safety filters. Finally, when logging the transaction for auditing or observability purposes, verify that your logging framework only captures the sanitized prompt and the model’s response. This guarantees that your cloud logs remain entirely free of PII, maintaining compliance with frameworks like GDPR, HIPAA, or CCPA.
Scaling and Auditing Your Secure AI Architecture
Transitioning a secure AI pipeline from a local proof-of-concept to an enterprise-grade production environment requires a robust strategy for scalability and observability. When integrating Regex and the Gemini API to handle Personally Identifiable Information (PII), your architecture must be designed to handle high-throughput data streams without introducing latency bottlenecks or security blind spots.
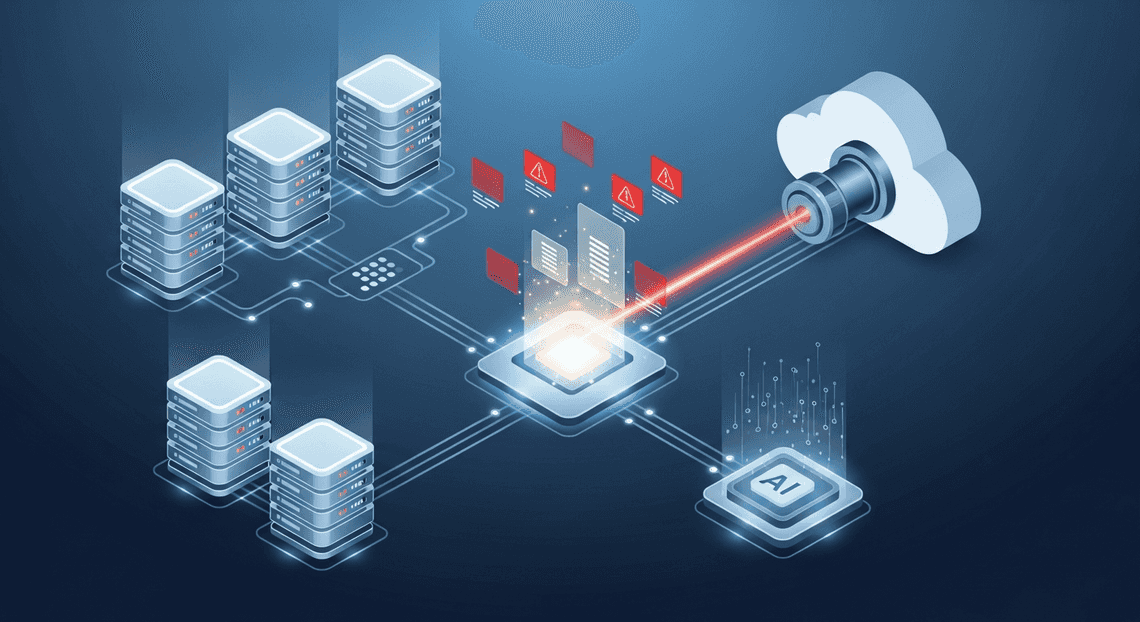
In a Google Cloud environment, deploying your PII redaction and AI processing logic via serverless compute options like Cloud Run or Cloud Functions is highly recommended. These services automatically scale out to handle sudden spikes in data ingestion—whether you are processing real-time customer support chats or batch-analyzing massive document repositories. To ensure asynchronous reliability, decouple your ingestion and processing layers using Pub/Sub. This allows your system to queue incoming text, apply Regex redaction, and safely pass the sanitized payloads to the Gemini API at a controlled rate, respecting quota limits.
Equally critical is your auditing strategy. You must maintain a verifiable trail of how data is processed to satisfy compliance frameworks like GDPR or HIPAA. Leverage Cloud Logging and Cloud Audit Logs to track metadata about the redaction process. Crucial note: Ensure your logging configuration is strictly designed to log the action of redaction (e.g., “Redacted 2 SSNs and 1 Email at timestamp X”) and the performance metrics (latency, Gemini API response times), without ever writing the raw, unredacted PII into the logs themselves.
Maintaining and Updating Regex Rules for Edge Cases
While regular expressions provide a lightning-fast, deterministic first line of defense for PII redaction, they are inherently rigid. Human data entry is messy, and PII formats constantly evolve. You will inevitably encounter edge cases—a newly formatted international phone number, an alphanumeric employee ID, or a creatively obfuscated email address—that your initial Regex patterns will miss.
To maintain a secure pipeline at scale, you must treat your Regex patterns as dynamic configurations rather than hardcoded strings buried in your application logic. Here are the best practices for managing this:
-
Decouple and Centralize Rules: Store your Regex dictionaries in a centralized, easily updatable repository like Firestore or Google Cloud Storage. This allows your security team to update patterns on the fly without requiring a full application redeployment.
-
Implement CI/CD for Regex: Regex updates can be dangerous. A poorly written pattern can lead to catastrophic backtracking (ReDoS attacks) or aggressive false positives that destroy the context needed by the Gemini API. Use Cloud Build to establish a CI/CD pipeline specifically for your Regex rules. Every new pattern should be automatically tested against a massive dataset of synthetic PII and non-PII text to validate its accuracy and execution time before being pushed to production.
-
Establish a Gemini Feedback Loop: Use the Gemini API as a secondary, intelligent safety net. If Gemini’s safety settings or natural language understanding flags a prompt for containing sensitive data that your Regex missed, build a mechanism to safely log this anomaly. This creates a continuous feedback loop, allowing your data engineering team to analyze the leaked edge case and write a new Regex rule to catch it in the future.
Book a Discovery Call with Vo Tu Duc for a Custom Architecture Audit
Securing AI pipelines is rarely a one-size-fits-all endeavor. The nuances of your specific data flows, compliance requirements, and existing Google Cloud infrastructure demand a tailored approach. If you are looking to integrate Large Language Models into your business operations but are hindered by data privacy concerns, expert guidance can bridge the gap.
As a Google Cloud and Workspace engineering specialist, I help organizations design, build, and scale secure AI architectures. Whether you need to optimize your current Regex-to-Gemini pipelines, implement enterprise-wide data loss prevention (DLP) strategies, or ensure your cloud environment adheres to the principle of least privilege, I can help.
Book a discovery call with Vo Tu Duc today for a comprehensive custom architecture audit. Together, we will review your current data ingestion workflows, identify potential PII vulnerabilities, and architect a highly scalable, compliant, and cost-effective Google Cloud solution that empowers your team to leverage the Gemini API with absolute confidence.
Stop Doing Manual Work. Scale with AI.
Want to turn these blog concepts into production-ready reality for your team?
Table Of Contents
Portfolios
Related Posts
Quick Links
Legal Stuff

